Understanding The Xen XSA-108 Security Issue
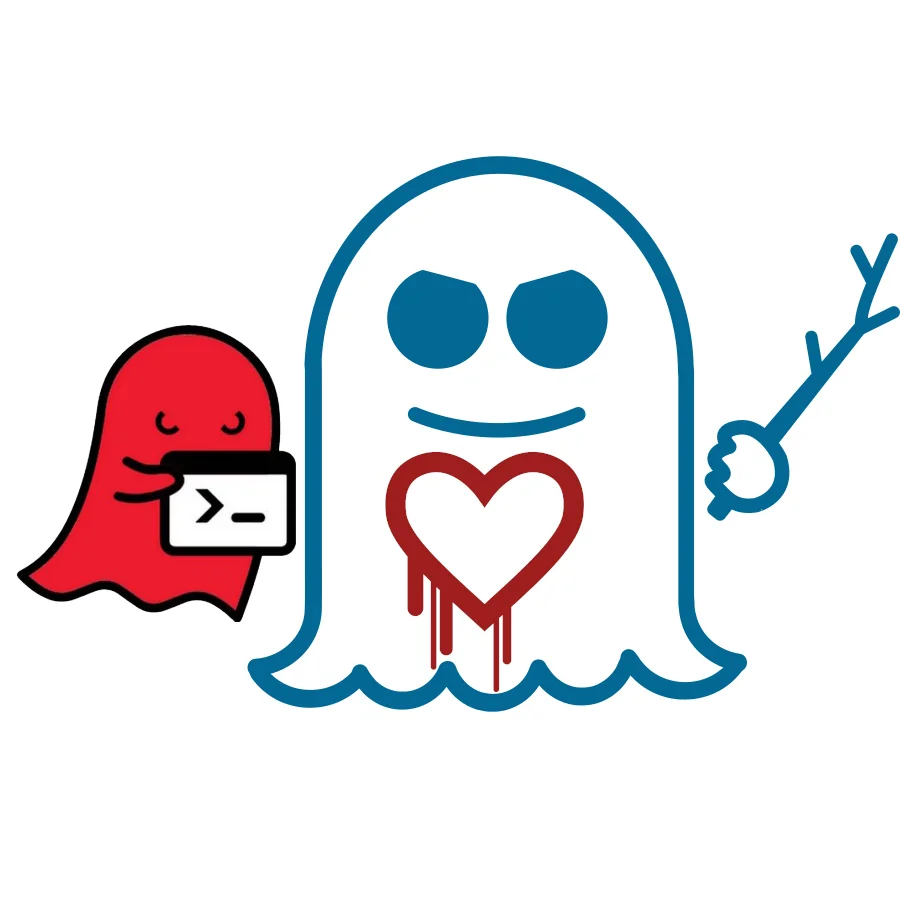
The XSA-108 issue could allow anyone with administrator access to a Xen HVM/PVHVM guest to crash the host or read portions of system's host memory -- either from another guest or the hypervisor itself. Like OpenSSL's Heartbleed bug, only a small amount of memory could be read at a time (up to 3KB) but could be read multiple times over.
Xen stakeholders wishing to learn more about the XSA-108 security issue now that it's no longer embargoed, head on over to the Xen Orchestra blog for their good write-up on the matter.
1 Comment

