XWayland Hit By Its First Security Advisory: Missing Authentication
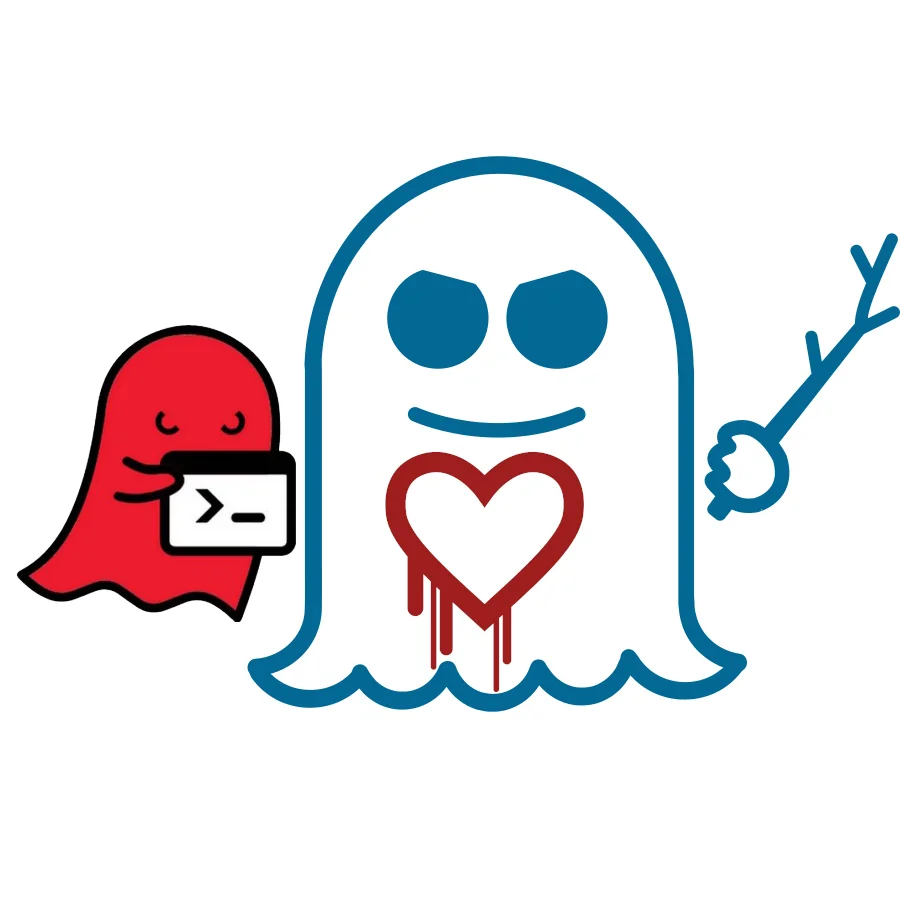
It turns out that the XWayland server currently starts up in a non-authenticating mode, thus any client with access to the server UNIX socket could connect to the server and use it. However, there's no Wayland compositors out there known to start XWayland with open TCP access, so at least remote exploits aren't expected. But this does mean that locally, untrusted users could capture input meant from other X11 clients, etc.
Fortunately, it's not a design flaw within Wayland but rather an issue with the XWayland DDX in the X.Org Server that's used by Weston 1.5+ and GNOME Shell/Mutter.
This CVE-2015-3164 issue is fixed in the latest X.Org Server Git code to be found in future X.Org Server 1.17 point releases and the 1.18 major release. More details in the advisory mailed out a few minutes ago by Daniel Stone.
5 Comments

