A commit made to the Linux kernel three weeks ago accidentally broke the default CPU security mitigations for non-x86 CPUs. With code sent in today via x86/urgent ahead of tonight's Linux 6.9-rc6 release, that accidental default breakage is being addressed.
Linux Security News Archives
283 Linux Security open-source and Linux related news articles on Phoronix since 2006.
A new set of Linux kernel patches were sent out on Friday for tweaking th Native BHI mitigation introduced earlier this month for Intel processors.
The Linux 6.9-rc4 weekly test release is due out later today and ahead of that this week's "x86/urgent" material has been sent in that includes several patches for various x86 speculation mitigation fixes.
Disclosed back in March 2022 was Branch History Injection (BHI) as a new Spectre vulnerability affecting Intel and Arm CPUs. Then in July of 2022 were patches for Intel working on hardware-based prevention for Spectre-BHI attacks. Now two years later the Linux kernel is seeing mitigations added for the native Branch History Injection vulnerability given a new "Native BHI" variant.
Today's disclosure of XZ upstream release packages containing malicious code to compromise remote SSH access has certainly been an Easter weekend surprise... The situation only looks more bleak over time with how the upstream project was compromised while now the latest twist is GitHub disabling the XZ repository in its entirety.
Red Hat today issued an "urgent security alert" for Fedora 41 and Fedora Rawhide users over XZ. Yes, the XZ tools and libraries for this compression format. Some malicious code was added to XZ 5.6.0/5.6.1 that could allow unauthorized remote system access.
With security concerns at all-time highs in the industry, Linux 6.9 is seeing yet more work to beef up its security hardening with various additional safety checks and other compile-time defenses for ensuring security best practices.
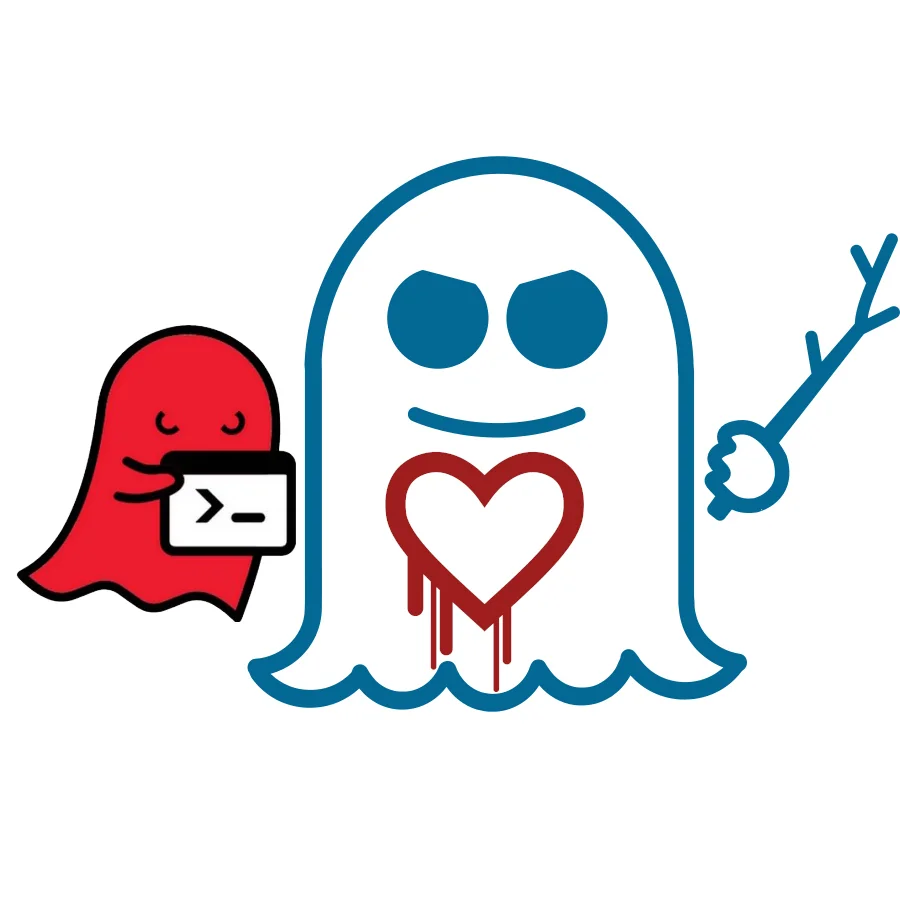
VUSec and IBM Research Europe today announced Speculative Race Conditions (SRCs) as a as a new class of vulnerabilities where thread synchronization primitives using conditional branches can be microarchitecturally bypassed on speculative paths using a Spectre-V1 attack. The researchers have dubbed CVE-2024-2193 as GhostRace and is said to affect all major CPU vendors.
The x86/core changes were submitted today for the now-open Linux 6.9 merge window. Among other changes, the x86 CPU security mitigation options within the Linux kernel Kconfig have been adjusted where appropriate to make more clear the options/features are for security mitigations.
While there is already the work underway on allowing the Rust programming language within the Linux kernel in part to leverage its memory safety potential, a proposal was sent out this morning for a new "SandBox Mode" for the Linux kernel to also increase the memory safety of C code within the kernel.
Kicking off what may end up being a fairly busy Patch Tuesday are two WiFi authentication vulnerabilities being made public that affect Intel's IWD daemon as well as the WPA_Supplicant software -- between the two they are the most common solutions for wireless daemons on Linux systems.
For those making use of the AppArmor Linux kernel security module, there is a notable change coming with the Linux 6.8 kernel.
The hardening updates for the Linux 6.7 kernel bring a new hardening configuration profile to help in building a security hardened kernel with some sane defaults.
The AppArmor Linux security system has picked up a few improvements and new features with the in-development Linux 6.7 kernel.
The widely-used Curl project as a command-line tool and library for transferring data via a variety of protocols is preparing to roll-out Curl 8.4 early in order to address a particularly nasty vulnerability.
Disclosed back in August was the Inception vulnerability affecting all Zen processors. It took until today though for the mainline Linux kernel to mitigate Hygon processors for this vulnerability for those Zen 1 CPUs formed from the AMD-Chinese joint venture.
A Red Hat engineer has published patches to optionally allow delayed module signature verification in an effort to have a secure Linux system but to allow for faster boot times.
Security Enhanced Linux (SELinux) has been part of the mainline kernel for two decades to provide a security module implementing access control security policies and is now widely-used for enhancing the security of production Linux servers and other systems. Those that haven't been involved with Linux for a long time may be unaware that SELinux originates from the US National Security Agency (NSA). But now with Linux 6.6 the NSA references are being removed.
To help harden the Linux kernel from memory vulnerabilities and in particular heap spraying, set to be merged into the Linux 6.6 kernel is optional support for randomized slab caches for kmalloc() calls.
There used to be a time when Patch Tuesday wasn't so busy in the Linux space, but certainly not this month... Linus Torvalds just pushed the kernel code changes around AMD INCEPTION and Intel DOWNFALL as well as other security patches.
It's now more clear why last week Linus Torvalds personally took to improving the Linux kernel's user-mode stack expansion code: it's necessary to address a now disclosed security vulnerability dubbed StackRot.
This week alongside several other Linux Foundation events in Vancouver was the Linux Security Summit. Commanding a significant presence at the Linux Security Summit was Microsoft.
In development for several years now has been TrenchBoot as a framework for creating security engines to perform system launch integrity actions. This boot-time integrity framework continues advancing and this past week Oracle engineers posted their latest patches for the Linux kernel in providing dynamic launch support.
With the Linux 6.4 kernel there is the ability being introduced so that the machine keyring can optionally only store CA-enforced keys.
After being deprecated for several years, Security Enhanced Linux "SELinux" beginning with the Linux 6.4 kernel can no longer be run-time disabled.
With the Linux 6.2 release kernel developers addressed "a tasty target for attackers" after it was realized that the per-CPU entry data was not being randomized, even in the presence of Kernel Address Space Layout Randomization (KASLR). The per-CPU entry area randomization has been present since Linux 6.3 but then was realized it's being activated even if KASLR was disabled, so now that is changing to avoid possible confusion.
Ahead of the Linux 6.3-rc1 release later today, a set of "x86/urgent" patches were sent out Sunday morning that include the change to allow Single Threaded Indirect Branch Predictors (STIBP) to be used in the presence of legacy Indirect Branch Restricted Speculation (IBRS) for security reasons.
The Linux kernel since last year has mistakenly left systems relying on the original Indirect Branch Restricted Speculation (IBRS) for Spectre V2 mitigation without Single Threaded Indirect Branch Predictor (STIBP) coverage for cross-HyperThread dealing with this Spectre vulnerability. There is a patch underway that is resolving this issue for Intel Skylake era systems.
Back in 2020 Google and the Open-Source Security Foundation (OpenSSF) came up with a "Criticality Score" to rank the importance/criticality of open-source projects. The Criticality Score is a means of quantifying the importance of an open-source project such as if in need of funding or development assistance. Criticality Score 2.0 has now been published.
Linus Torvalds merged to Linux 6.3 Git the TPM CRB support for Microsoft's controversial Pluton security co-processor that is initially found in the latest AMD Ryzen processors.
A proposed Linux kernel patch would provide a new Kconfig build time option of "CONFIG_DEFAULT_CPU_MITIGATIONS_OFF" to build an insecure kernel if wanting to avoid the growing list of CPU security mitigations within the kernel and their associated performance overhead.
Merged back in Linux 5.13 last year was Landlock for allowing unprivileged application sandboxing. Landlock allows restricting ambient rights for a set of processes and is implemented as a stackable Linux security module (LSM) for establishing safe security sandboxes. With Linux 6.2 file truncation support is added for Landlock.
Intel on Sunday posted a set of Linux patches implementing SPEC CTRL virtualization support for this VMX feature with new Intel CPUs to help with migrating virtual machines to hosts with different CPU microarchitectures where their security mitigations may be different.
As an enhancement to the out-of-the-box Linux kernel in its default x86_64 configuration, it was being eyed to enable Indirect Branch Tracking by default. That change to enable IBT by default has been picked up by TIP's x86/core branch, thus putting it on deck as material for submitting with next month's Linux 6.2 merge window.
Indirect Branch Tracking (IBT) is still being eyed for enabling as part of the default Linux x86_64 kernel configurations to provide better out-of-the-box security on supported processors. A patch sent out today continues the upstream discussion over flipping on this feature by default that is part of Intel's Control-flow Enforcement Technology (CET) for helping to defend against jump/call oriented programming attacks.
Two high severity security vulnerabilities affecting OpenSSL were made public today, which were the issues that led to Fedora 37 being delayed to mid-November to allow the release images have mitigated OpenSSL packages.
Back in August 2021 saw initial patches by Intel for "FineIBT" for the Linux kernel as aiming to combine the best of their Control-flow Enforcement Technology (CET) and Control Flow Integrity for upping the kernel security protections in an efficient manner.
While the Linux 6.1 merge window just passed and the "Call Depth Tracking" patches have been in development the past few months, it looks like that for the Linux 6.2 kernel is where that alternative mitigation technique will be introduced for helping offset some of the significant performance regressions incurred for Intel Skylake era processors as a result of recent CPU security vulnerability mitigations.
Git 2.38.1 was just released along with updates to older versions, including the new point releases of v2.30.6, v2.31.5, v2.32.4, v2.33.5, v2.34.5, v2.35.5, v2.36.3, and v2.37.4. The big set of Git updates today is due to two more security issues coming to light.
This morning's batch of Linux kernel point releases to existing stable series is worth upgrading to given the important security fixes.
In addition to MGLRU and Maple Tree having been merged overnight, Linus Torvalds also picked up the x86/mm changes for Linux 6.1 that will now by default warn about W+X mappings.
The x86/core changes for Linux 6.1 have been merged and are headlined by making sure an INT3 instruction is inserted after every unconditional Retpoline jump (JMP) for the Retpolines handling on both Intel and AMD processors.
The Security Enhanced Linux (SELinux) changes for Linux 6.1 but with a documentation update does provide a good reminder for a public service announcement: run-time disabling of SELinux is deprecated and will be removed in the future.
A kernel hardening security improvement on the way for Linux 6.1 is the ability to provide warning of possible memcpy() based overflows. Right now this is only a warning but it's work towards being able to address "trivially detectable" buffer overflow conditions within the kernel and in the future may be able to block such overflows from happening.
Over the summer Jason Donenfeld of WireGuard fame proposed adding getrandom() to the vDSO for better performance to enjoy by user-space developers. This past week he sent out the latest version of this proposed kernel patch where he's seeing around a ~15x speed-up with this change.
Proposed a few years ago was Kernel Address Space Isolation (KASI / ASI) for limiting data leaks with the growing number of speculative execution attacks on CPUs. Several organizations have been involved with Address Space Isolation efforts for the Linux kernel including IBM, Oracle, and Google with various approaches. Google engineers earlier this year posted a newer iteration of ASI focused on KVM use for the cloud / VMs. ASI still hasn't made it to the mainline kernel but Google engineers this week at LPC argued that it should be the path forward for mainline in better dealing with these CPU security vulnerabilities.
Longtime Linux kernel engineer Peter Zijlstra with Intel has sent out his latest "Call Depth Tracking" patches as a mitigation for Retbleed that aims to be less costly on system performance than the current mitigation approach. With this latest patch series, he indicates he hopes to soon get this code mainlined.
Back in July Intel's Peter Zijlstra proposed "Call Depth Tracking" as a mitigation approach for handling Retbleed and avoiding the "performance horror show" of Indirect Branch Restricted Speculation (IBRS) usage. Out today is the newest version of the Call Depth Tracking code and the performance benchmark results are looking very promising for lessening the pain of the Retbleed CPU mitigation performance impact.
In addition to being busy leading WireGuard, Jason Donenfeld continues working heavily on the Linux kernel's random number generator (RNG) code. For Linux 6.0, a number of RNG improvements are ready.
While relevant Intel and AMD processors have been mitigated for the recent Retbleed security vulnerability affecting older generations of processors, those mitigations currently just work for x86_64 kernels and will not work if running an x86 (32-bit) kernel on affected hardware. But it's unlikely to get fixed unless some passionate individual steps up as the upstream developers and vendors have long since moved on to just caring about x86_64.
283 Linux Security news articles published on Phoronix.
