FreeBSD Finally Gets Mitigated For Spectre & Meltdown
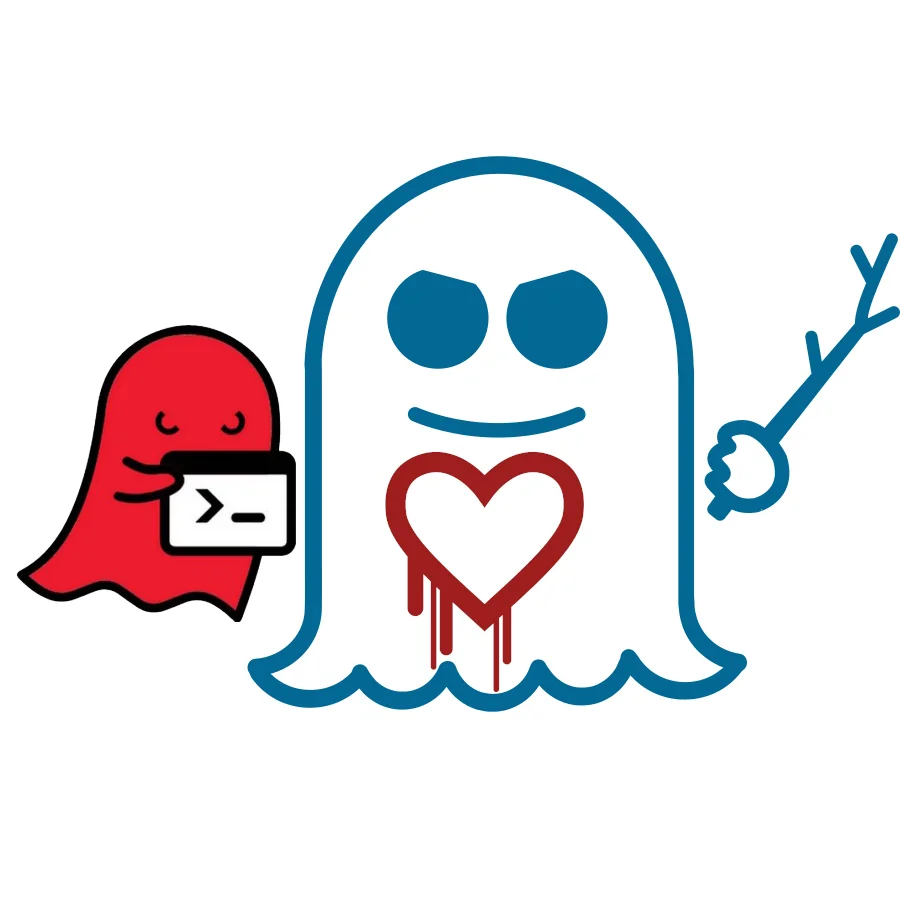
It's taken a few more weeks longer than most of the Linux distributions to be re-worked for Spectre/Meltdown mitigation as well as DragonFlyBSD, but with FreeBSD Revision 329462 it appears their initial fixes are in place.
There is Meltdown mitigation for Intel CPUs via a KPTI implementation similar to Linux, the Kernel Page Table Isolation. There is also a PCID (Process Context Identifier) optimization for Intel Westmere CPUs and newer, just as was also done on Linux.
For their Spectre mitigation they are currently making use of IBRS: Indirect Branch Restricted Speculation. The IBRS feature just as with Linux requires support from the CPU microcode and is for mitigating the Variant Two vulnerability as an alternative to Retpolines.
Their stable 11 code can be found here. Given the severity of Spectre and Meltdown, I wouldn't be surprised if they end up shipping a new stable point release soon.
160 Comments

