NXP PowerPC Processors Finally Being Mitigated Against Spectre V2 With Linux 4.21
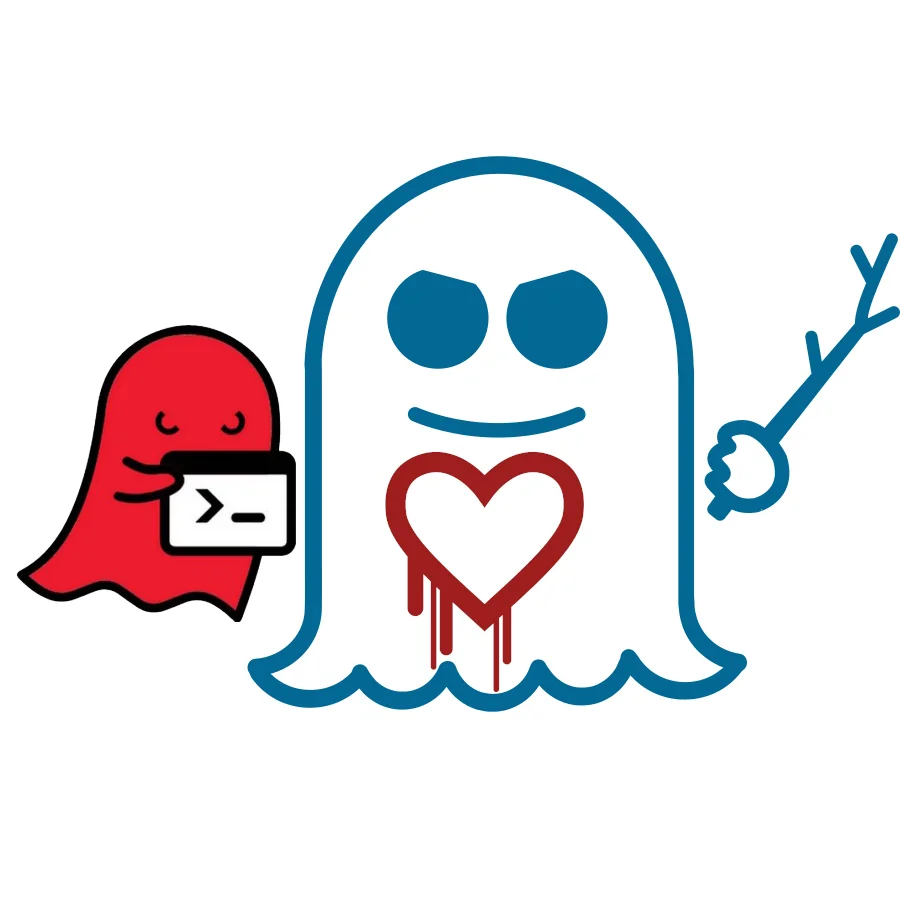
Queued for merging into Linux 4.21 is the Spectre V2 mitigation for these NXP PowerPC Book3E processors. Their approach is to flush the branch predictor whenever the privilege level has changed or kernel entry to protect user-space to user-space attacks and user-space attacks against the kernel. In the case of KVM virtualization, the branch predictor is flushed as well at each KVM entry.
For those that want to forego this mitigation to avoid the likely performance impact, the code does support a no_spectrev2 kernel command line parameter (the same as on x86-based platforms) that won't enforce this frequent branch predictor flushing.
NXP developers working on this Spectre V2 mitigation hadn't shared any of their expected performance costs of this mitigation.
The mitigation is landing as part of the PowerPC changes. That pull also has POWER DMA code changes, support for generating their system call tables from a text file, fixes to the transactional memory support, and other low-level changes.
1 Comment

